By Beau Hodai, December 30, 2012
Jump to source materials archive for this article.
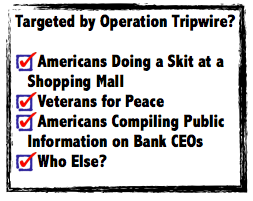
 Records obtained from the Federal Bureau of Investigation (FBI) by DBA Press and the Center for Media and Democracy (DBA/CMD) through a Freedom of Information Act (FOIA) request indicate that the FBI employed tactics under a “counter terrorism” initiative called “Operation Tripwire” in the monitoring of Occupy Wall Street (OWS) activists.
Records obtained from the Federal Bureau of Investigation (FBI) by DBA Press and the Center for Media and Democracy (DBA/CMD) through a Freedom of Information Act (FOIA) request indicate that the FBI employed tactics under a “counter terrorism” initiative called “Operation Tripwire” in the monitoring of Occupy Wall Street (OWS) activists.
[Note: records referenced in this article were obtained by DBA/CMD on November 8, 2012, as a partial response to a FOIA request submitted by DBA/CMD to the FBI on June 7, 2012. DBA/CMD have been analyzing these incomplete materials along with other public records to tell a more complete story of the pattern of domestic surveillance that has been underway.]
“Tripwires,” Mall Cops, and “Radical Cheerleaders”
 On October 19, 2011, an FBI agent filed a report, titled “Domain Program Management [,] Domestic Terrorism,” detailing an October 11 briefing given to “Jacksonville Executive Management” (EM) and a supervisory special agent (SSA) “Counter Terrorism Program Coordinator.” The subject of the October 11 briefing had been the potential growth of the OWS movement throughout north/central Florida. (All agent names were redacted from this, and other, FBI reports.)
On October 19, 2011, an FBI agent filed a report, titled “Domain Program Management [,] Domestic Terrorism,” detailing an October 11 briefing given to “Jacksonville Executive Management” (EM) and a supervisory special agent (SSA) “Counter Terrorism Program Coordinator.” The subject of the October 11 briefing had been the potential growth of the OWS movement throughout north/central Florida. (All agent names were redacted from this, and other, FBI reports.)
“During the 11 October intelligence meeting, writer advised EM of the Occupy venues and further advised that they may provide an outlet for a lone offender exploiting the movement for reasons associated with general government dissatisfaction,” wrote the agent, who went on to say that special areas of concern were Daytona, Gainesville, and Ocala, where “some of the highest unemployment rates in Florida continue to exist.”
As such, the report’s author recommended that the Counter Terrorism Program Coordinator, “consider establishing tripwires with the Occupy event coordinators regarding their observance of actions or comments indicating violent tendencies by attendees” (emphasis added).
Occupy Gaineville cheerleaders were targeted by Tripwire.
Interestingly, the report went on to discuss the author’s sharing of information obtained from the FBI Houston field office– as an example of such potential “exploitation”– with the Jacksonville Counter Terrorism Program Coordinator. The FBI Houston information related to the “exploitation” of Occupy Houston by an individual (name redacted) who had allegedly plotted to “kill local Occupy leaders via sniper fire.” (It is worth noting here that one of the few other instances of a credible threat identified by the FBI in relation to OWS contained in the DBA/CMD FOIA records relates to an October 2011 instance in which a person reportedly threw a “chemical bomb” made from tinfoil and Drano at “Occupy Maine” protestors after shouting “get a job!”)
According to the FBI, “Operation Tripwire,” established in 2003, focuses on “information and intelligence-sharing operations from the NJTTF’s [National Joint Terrorism Task Force] participating agencies to help identify terrorist sleeper cells in the U.S.” Such information is obtained through intelligence provided by various private sector “critical infrastructure stakeholders,” along with apparent networks of informants established through regional JTTF “community outreach” activities.
An example of Tripwire’s intended use at the time of its inception is as follows: a suspicious pattern of chemical purchases might be provided to the FBI by a merchant. This information would be relayed from the regional JTTF to NJTTF.
NJTTF, originally situated within the FBI Strategic Information and Operations Center (SIOC, the same FBI office that issued a request for information to vendors in January 2012 for the development of a social media application capable of trolling Facebook, Twitter, and other social media for certain keywords and other information), is currently situated within the National Counter Terrorism Center (NCTC). NCTC, an entity of the Office of the Director of National Intelligence (ODNI), is the nation’s lead agency on “counter terrorism” intelligence information sharing. NCTC is comprised of staff from partner intelligence agencies. Such agencies include: the Central Intelligence Agency (CIA), FBI, Department of Defense (DoD) and the Department of Homeland Security.
“Tripwire” information provided to NJTTF by the merchant informant would then be evaluated, possibly investigated, and shared with other NJTTF/”counter-terrorism” personnel.
According to the FBI, NJTTF is comprised of representatives from at least 35 law enforcement/”public safety” agencies. This counter-terrorism intelligence cooperative is fed information through the nation’s 104 JTTFs (which work, in turn, with regional law enforcement agencies through state “fusion centers”), each of which may gather intelligence through tactics employed under Operation Tripwire. In practice, this equates to the cultivation of informants, the sharing of FBI intelligence with commercial informants, and the gathering of information about people without any predicate of wrongdoing by them. FBI investigatory thresholds were lowered by the executive branch during the George W. Bush administration, however it is not entirely clear what investigative guidelines/thresholds Operation Tripwire is operating under.
Although the October 19 FBI briefing report seems to describe the potential application of Operation Tripwire in the cultivation of informants within the north/central Florida OWS community, another Florida FBI report relating to OWS activities shows that business sector “tripwire” informants were utilized in the Gainesville area for the purpose of monitoring local OWS activity. The report shows that advance intelligence relating to OWS protests was provided to this business sector tripwire informant, who was expected to reciprocally supply independently gathered information.
In the December 5, 2011 FBI Jacksonville report, titled “Trip Wire Initiative [,] Intel Briefing/Squad 7 [,] Gainesville Resident Agency,” the report’s author documents contact with a security employee at Gainesville’s The Oaks Mall, in reference to an upcoming OWS protest event.
“On 11/10/2011, the writer telephonically contacted [redacted] The Oaks Mall, at telephone number [redacted]. The purpose of the contact was to advise her of the pending ‘Occupy Wall Street’ protest which was scheduled to shut-down various banks on 1/17/2011 [sic],” wrote the report’s author.
“[Redacted name of mall security employee] advised that the initial Occupy Gainesville protest was a minor distraction for the mall and she would be ready for the pending protest. [Redacted] advised that she would contact writer if there were any anomalies.”
On October 30, 2011, nine members of Occupy Gainesville (the “Occupy Gainesville Radical Cheerleaders”) appeared in the cafeteria of The Oaks Mall and performed a corporate greed-themed dance/cheer routine (a popular form of entertainment and/or protest known as a “flash mob”). The dance group, which consisted of college-aged adults, was asked to leave by mall security following the completion of the routine. During this interaction, mall security personnel tried to ascertain the names of the cheerleaders.The group declined, politely, to provide their names, thanked the security officer and promptly left.
The following month, as reported by the Gainesville Sun, a group of about a dozen individuals, identified as being members of Occupy Gainesville, entered The Oaks Mall on the morning of November 25, 2011 (“Black Friday”) and began chanting slogans. Mall security asked the group to leave. The group promptly left.
It is not clear if Occupy Gainesville ever returned to The Oaks Mall.
It is not clear how this application of federal law enforcement time and resources through Operation Tripwire benefits non-commercial interests within the United States in any way, let alone efforts to protect the nation from a terrorist attack.
FBI records obtained by DBA/CMD go on to discuss the JTTF monitoring of OWS groups in northern and central Florida. The primary objects of this surveillance appear to have been Occupy Gainesville and Occupy Tampa. The two groups had coordinated with each other in a number of events– including dance events staged by the Occupy Gainesville “Radical Cheerleaders.”
As such, a November 4, 2011 FBI report entitled “Domestic Terrorism Control File [,] Liaison [,] Field Intelligence Group [,] Liaison Matter” states that, during a November 3 “Tampa Bay Area Intelligence Unit” briefing, various representatives from area law enforcement agencies discussed numbers of attending OWS protestors at peaceful bank protests that had occurred on October 29.
Also discussed during the briefing, wrote the report’s author (a member of the Tampa JTTF, name redacted), were suspected firearms purchases by members of the Pagan Motorcycle Club, the burglary of 50 storage units, and a string of robberies in the Tampa area. Those issues, however, were only peripheral subjects of interest to the JTTF, as is evidenced by the amount of evident discussion dedicated to the subject of area OWS activists.
The Tampa JTTF report went on to state that the Hillsborough County Sheriff’s Office had determined certain individuals (names redacted) to be the leaders of Occupy Tampa, and that these individuals would be traveling to Gainesville for an “anarchist planning meeting at the Civic Media Center” on November 5.
The report went on to indicate that the JTTF/Tampa Bay Area Intelligence meeting had closed with a briefing from Air Force Office of Special Investigations (AFOSI) personnel. According to AFOSI, Veterans for Peace had invited Occupy Tampa and Occupy St. Petersburg to join them in an anti-war demonstration outside of one of the MacDill Air Force Base gates during “Air Fest,” to be held on November 5 and 6.
The Occupy Threat? “Disrupt” and “Dox”
But, what was the perceived threat that may have prompted the application of Operation Tripwire to OWS activists? Records cite two themes of perceived OWS threats: the possible disruption of “normal business operations of financial districts” and the possible embarrassment of bankers. A critical mind might wonder what either of these two perceived threats has to do with “terrorism.”
Speaking to the perceived threat of disruption, FOIA records obtained from the FBI by DBA/CMD indicate that the bureau had been in the business of alerting financial institutions to the planned protest activity of OWS groups as early as August 2011– nearly a month prior to the launch of the OWS movement on September 17, 2011.
Records indicate that on August 19, 2011, an FBI task force officer (TFO) met with a representative of the New York Stock Exchange (described as “NYSE/Euronext,” located at 11 Wall Street, New York City) to discuss the “planned Anarchist protest titled ‘Occupy Wall Street’, [sic] scheduled for September 17, 2011.” (Which task force the agent represented is unknown due to redactions.)
“The protest appears on Anarchist website’s and social networking pages on the internet [sic],” wrote the TFO.
“Numerous incidents have occurred in the past which show attempts by Anarchist groups to disrupt, influence, and or shut down normal business operations of financial districts,” claimed the TFO.
And, speaking to the looming specter of banker embarrassment: FBI records obtained by DBA/CMD, show that, on October 6, 2011, an FBI intelligence analyst (IA) contacted security personnel with Zions Bank, based in Salt Lake City, to warn of an alleged “possible threat posed by hacktivist Anonymous” posed to Zions Bank executives. Occupy Salt Lake City had been formed the very day the FBI delivered this warning to Zions Bank.
“Anonymous” is the name of a collective of internet-based activists, who are said to be hackers, and who have largely aligned themselves with the OWS movement.
“IA [name redacted] informed [redacted name of Zions Bank security personnel] that the FBI had no specific intelligence indicating a specific threat to Zions Bank; however, the FBI wanted to make surein [sic] light of the upcoming Salt Lake City protestthat [sic] Zions Bank information security personnel were aware of recent hacking incidents perpetrated by Anonymous hacktivists in support of the Occupy Wall Street protest” (emphasis added).
“IA [redacted] informed [redacted name of Zions Bank security personnel] that the CEOs of Goldman Sachs and JP Morgan Chase had been ‘doxed’ by an actor claiming Anonymous affiliation. IA [redacted] explained that doxing is Internet slang for maliciously releasing public [sic] information regarding an individual on the Internet.”
The use of the word “public” before the word “information” in this report’s description of the so-called “doxing” of JP Morgan Chase President/CEO Jamie Dimon and Goldman Sachs CEO Lloyd Blankfein is not a typo. The “actor claiming Anonymous affiliation” referenced in this report posted data sheets listing nothing but publicly-available information about Dimon and Blankfein to Pastebin.com on September 27 and 29, 2011 (respectively). Such information contained in the short Dimon and Blankfein documents included the names of family members, some of the executives’ known addresses, some details from corporate filings, some records of campaign finance contributions, and some court records.
All of this material is available to anyone as a matter of public record. Information relating to an individual’s family members can be obtained through a number of public records (including birth records, property records, court records . . . and Google searches); addresses can be obtained through a number of public records (including campaign finance records, property records, court records and corporate records); corporate filings can be obtained through a number of public sources (primarily through the offices of secretaries of state/corporation commissions and the U.S. Securities and Exchange Commission); public records relating to campaign finance spending can be obtained through either state elections offices/secretaries of state, or the Federal Election Commission; and court records are typically obtained from publicly-funded courts of public (civil and criminal) law– whose records are generally a matter of public record.
Given the fact that neither the alleged “hacktivist” postings, or available FBI records, indicate any criminal activity related to the collating and posting of public information, it is likely that no “hacking incidents” took place– as is claimed in the Zions Bank FBI report.
As demonstrated by this report, FBI “intelligence analysts” apparently made it their business to notify bank executives that “actors” sympathetic with entities sympathetic to OWS might post public records relating to executives online. This is not a criminal offense. As a matter of course, journalists (journalists who are worth a damn, at least) utilize all of the aforementioned public records in research and reporting on a daily basis.
Given this fact, it is interesting to note that the portion of the report that details how such “actors” gather their data is entirely redacted.
Part Two is forthcoming.







Thank you for spreading the word. Edchaos. Occupy Gainesville media team.